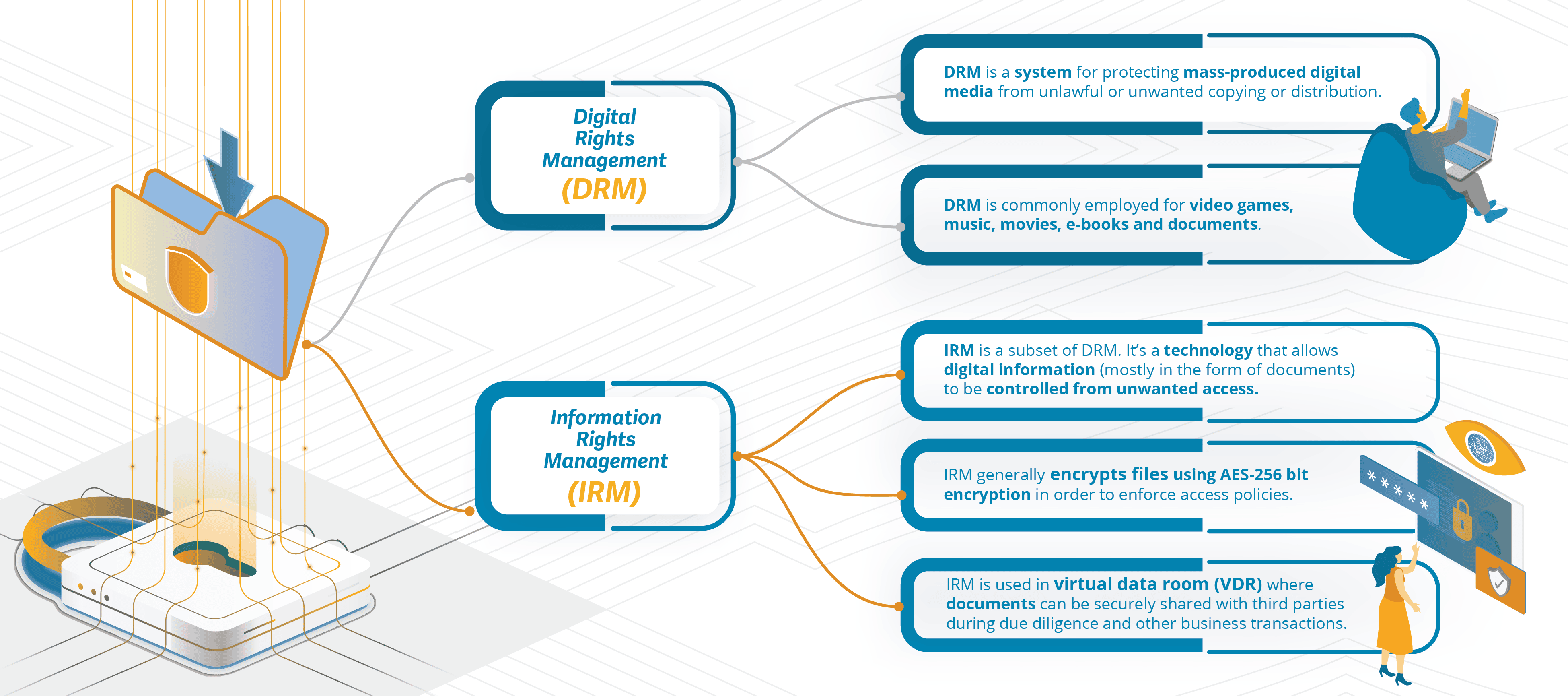
WHAT IS DIGITAL RIGHTS MANAGEMENT (DRM)?
Digital Rights Management (DRM) is a system for protecting mass-produced digital media from unlawful or unwanted copying or distribution. DRM is often associated with video games where the developer has put measures in place (by embedding code) to prevent users from copying the game or installing it on an unlimited number of devices. DRM is also commonly employed for music, movies, e-books and documents.
The Digital Millennium Copyright Act (DMCA), passed on October 12, 1998 and signed into law by President Clinton on October 28, 1998, amended Title 17 of the United States Code to extend the reach of copyright, while limiting the liability of the providers of online services for copyright infringement by their users. The new law essentially criminalized the use of techniques intended to circumvent DRM technology. The law also criminalizes the act of circumventing an access control, whether or not there is actual infringement of copyright itself.
DRM technology has been controversial in some circles, sometimes being called anti-competitive. DRM has also been criticized for restricting normal use of something legitimately purchased by the user.
WHAT IS INFORMATION RIGHTS MANAGEMENT (IRM)?
Information Rights Management (IRM) is a subset of DRM. It's a technology that allows digital information (mostly in the form of documents) to be controlled from unwanted access.
IRM generally encrypts files using AES-256 bit encryption in order to enforce access policies. Once encrypted, additional IRM rules can be applied to a document to allow or deny specific activities.
A common application that employs IRM is a virtual data room (VDR). A virtual data room is an online repository of information where documents can be securely shared with third parties during due diligence and other business transactions.
Administrators of a virtual data room can grant different individuals or groups varying levels of access to the VDR and, using Information Rights Management, can define what users are able to do with different documents. For instance, some documents might be designated as "Read Only" while others might be able to be downloaded.
Information Rights Management technology also gives administrators the ability to define if users are able to print, save, copy/paste, take screenshots, and whether a watermark should be applied. Because documents protected with IRM can only be opened with an active virtual data room connection, the permission of a user to open a document can be revoked retroactively. In this way, documents can be "remotely shredded", even after they've been downloaded.
HOW DOES INFORMATION RIGHTS MANAGEMENT PROTECT DOCUMENTS?
One of the common complaints about information rights management solutions is that they often require the user to have specialized IRM software installed on their computer in order to open files with IRM protection. These "plug-ins" can be frustrating to users and slow down the document review process. When evaluating an IRM solution, look for one that incorporates plug-in free technology that is fast and simple for users to employ.
Despite the fact that IRM technology can be a powerful force in securing sensitive documents when they're shared with third parties, no solution is 100% effective and there are some simple workarounds that can negate the benefits of IRM technology.
Suppose someone is viewing a confidential document that is protected with Information Rights Management technology and it has been designated as a "Read Only" document. This means the users cannot save, print, edit, copy/paste or print to PDF. They can view the document, but nothing else. And, because this document can only be opened with an active VDR connection, it means that the administrator of the VDR has complete control over the document and can revoke access to it at any time.
But what's to prevent a user from taking a screenshot of the document and capturing a permanent image of it? Some VDR providers have anticipated this and built in added functionality that prevents screenshots, even by third party software (such as SnagIt) that provide screen capture capabilities. When choosing a virtual data room provider for information rights management, make sure to select one that prevents screenshots.
Sometimes the people you share documents with will insist (especially lawyers) that they are able to print the documents. This is when applying a watermark can be beneficial. A watermark is clearly visible, applied diagonally across the page, yet does not interfere with the readability of the underlying text.
The watermark can be dynamic and fully customizable and can include:
- The user's name
- Company name
- Email address
- IP address
- And even the date and time the document was opened.
Watermarks provide a clear reminder to the reader that the content is confidential, and since the user's identity is included in the watermark, it provides a simple, but effective, deterrent against unauthorized distribution of the printed documents.
WHAT ABOUT POPULAR FILE SYNC AND SHARE PLATFORMS AND IRM?
File sync and share platforms (FSS) have become enormously popular, both for individual and business use. FSS platforms are great for sharing photos with family and friends or business files with colleagues for collaboration. They're also great for storing and syncing files across devices, and they offer best-of-breed features for collaborative authoring and editing.
But most file sync and share tools have evolved from consumer-grade file sharing and therefore don't have the features needed to maintain complete control of content after it's been shared.
That's because they don't offer Information Rights Management. Consumer file sync and share platforms can only protect your documents while they remain within their storage cloud. Once a document is shared with another user, the security ends and control is lost.
So, when it becomes necessary to share confidential information with parties outside of an organization, such as during due diligence, a more robust platform that employs IRM, such as a virtual data room, is recommended.
In response to the popularity of file sync and share platforms, and knowing that there are times when confidential information needs to be shared with parties outside the organization, some VDR providers have developed connectors to popular file sync and share platforms enabling seamless integration with Box, Dropbox, SharePoint, Office365 and Docusign.
Users can add multiple connectors to aggregate content from different organizations so their external users can log in to one online repository and securely access content from all of the user's various cloud-based platforms.
These FSS connectors require no additional software to be installed and enable users to easily upload file structures and documents from their existing FSS platforms to the virtual data room where they then enjoy all the security and Information Rights Management features that a virtual data room provides, including the ability to prevent saving and printing, the application of customizable watermarks, blocking screenshots and the ability to "remotely shred" documents, even after they've been downloaded.
File sync and share platforms are great for sharing business files with colleagues for collaboration and for syncing files across devices, but when sharing confidential or sensitive documents with outside parties those documents need to be controlled with the features that only IRM provides.
ShareVault has been providing organizations of all types and sizes with secure document sharing solutions for over 15 years.
