A security audit is an essential process that helps organizations identify potential security threats and vulnerabilities in their systems, processes, and procedures. In today’s world of burgeoning cyber crime, it’s increasingly critical for organizations to take the threat seriously and conduct regular security audits. However, conducting a security audit requires a comprehensive approach to ensure that all possible security gaps are identified and addressed. We’ve developed a 7-step list that will ensure your next security audit is conducted appropriately and achieves its objectives.
1. Define the scope and objectives
The first step in conducting a security audit is to define the scope and objectives of the audit. This involves identifying the assets and processes that will be audited, as well as the goals and objectives of the audit. For example, the audit may be focused on assessing the security of a specific application, or it may be a comprehensive review of all security-related processes in the organization.
2. Identify the audit team
The next step is to identify the audit team. The audit team should be composed of individuals who have experience and expertise in conducting security audits. The team may include internal staff, external consultants, or a combination of the two. It’s important to ensure that the audit team has access to all the necessary information and resources required to conduct the audit.
3. Gather information
The audit team should gather information about the systems, processes, and procedures that are being audited. This may include reviewing documentation, interviewing staff, and conducting technical assessments of the systems. The information gathered should be used to identify potential security gaps and vulnerabilities.
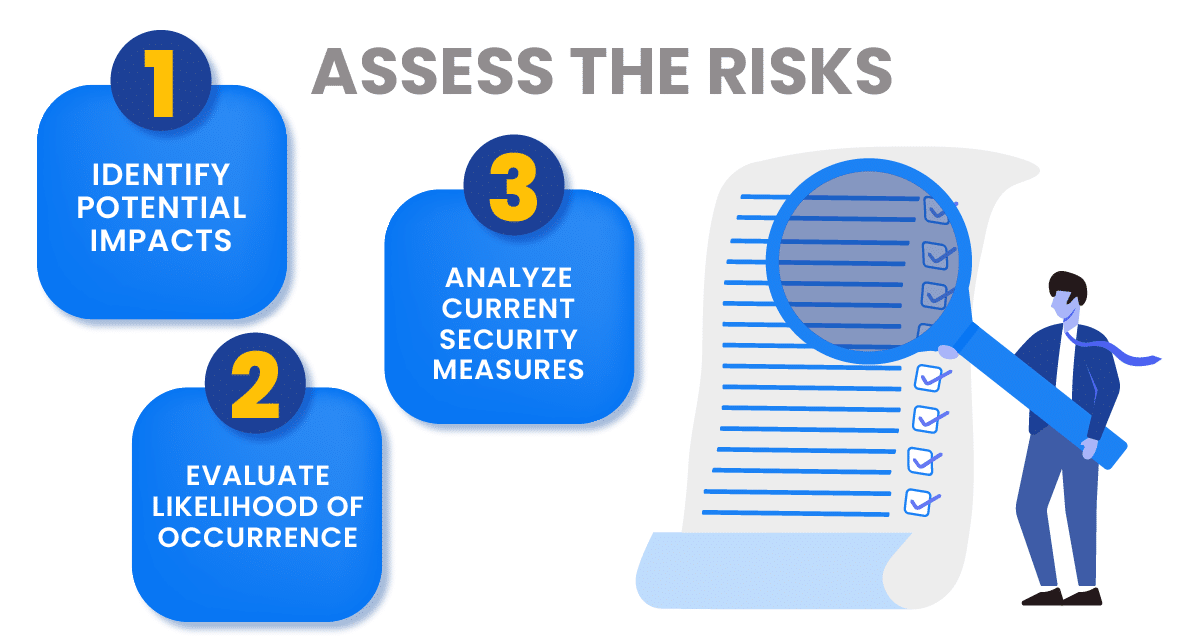
4. Assess the risks
Once the information has been gathered, the audit team should assess the risks associated with the systems, processes, and procedures being audited. This involves identifying the potential impact of a security breach, the likelihood of a breach occurring, and the effectiveness of current security measures in mitigating the risks.
5. Identify security gaps and vulnerabilities
Based on the information gathered and the risk assessment, the audit team should identify security gaps and vulnerabilities. This may include identifying weaknesses in passwords, inadequate security controls, precarious employee behavior, or vulnerabilities in software or hardware.
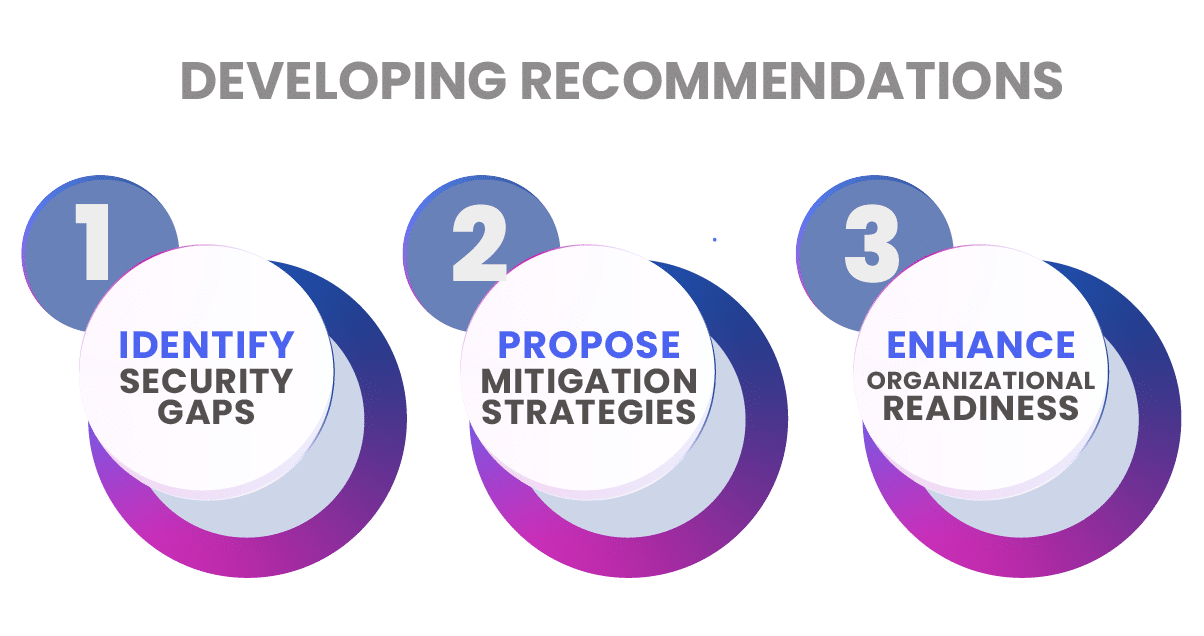
6. Develop recommendations
The audit team should develop recommendations for addressing the security gaps and vulnerabilities identified during the audit. These recommendations may include implementing new security controls, updating software or hardware, or improving staff training.
7. Present findings and recommendations
The final step is to present the findings and recommendations to the relevant stakeholders in the organization. This may include senior management, IT staff, and other relevant parties. The findings and recommendations should be presented in a clear and concise manner, and any questions or concerns should be addressed.
In conclusion, conducting a security audit is a complex and important process that requires careful planning and execution. By following the steps outlined in this article, organizations can ensure that they identify and address potential security threats and vulnerabilities, and improve the overall security of their systems, processes, and procedures.