Act now to protect your law firm from a cyber breach
03 November, 2021“Zero Trust” Document Security
Act now to protect your law firm from a cyber breach.
The promise of confidentiality is a cornerstone of the legal profession. The U.S. legal system provides numerous safeguards to protect attorney-client privilege. But who is going to protect confidentiality from a cybersecurity attack?
Hackers increasingly target law firms.
The number of security breaches at law firms is increasing. Recent hacks include:
- In February 2021, ransomware hackers broke into the operating system of Campbell Conroy & O’Neil, accessing documents and confidential information, including Social Security numbers, medical records, and financial account numbers. The firm’s clients include Boeing, Coca-Cola, FedEx, Exxon Mobil, Johnson & Johnson, and Walgreens. The amount of ransom was not disclosed.
- In June 2020, the REvil ransomware group breached the files of Grubman Shire Meiselas & Sacks, accessing a terabyte of information including personal files of high-profile clients like Mariah Carey, Lady Gaga, LeBron James, Nicki Minaj, and Donald Trump. The firm refused to pay the $42 million ransom.
- Also in June 2020, the REvil group infiltrated the operating system of IP law firm Vierra Magen Marcus, stealing 1.2 terabytes of data including patent agreements, business plans, NDAs, and correspondence, which they auctioned on the dark web.
- A third attack by the REvil group in 2021 breached Louisiana’s Fraser Wheeler & Courtney LLP, making with 50GB of confidential data, including client and customer information. The hackers ransomed the data at a starting price of $30,000.
- To date, the largest ransomware attack on a law firm was the 2017 hack of Mossack Fonseca, a Panamanian law firm that services off-shore accounts for a number of U.S. corporations, prominent politicians, and high-worth individuals. Hackers used a WordPress login and email server to steal 11.5 million files. To boost the value of their ransom demands, the hackers leaked files to the media, which led to questions about tax evasion. Harmed by the ransom costs and stain to their reputation, Mossack Fonseca closed its doors within two years of the attack.
Hackers target smaller law firms, too.
The ABA’s 2020 Legal Technology Survey reports that the number of firms experiencing a data breach increased to 29 percent, compared to 26 percent the year earlier. The same report goes onto report that just 34 percent of firms have an incident response plan in place, despite the risk of failure to meet information and consumer data privacy regulations, including New York’s Stop Hacks and Improve Electronic Security Act (SHIELD) and California’s Consumer Privacy Act (CCPA).
Ransomware hacks are expensive.
Legal field cybersecurity firm Coveware produced a Q1 2021 report revealed alarming statistics on the financial impact of ransomware:
- Average ransom payment was $220,298 (+43% from Q4 2020)
- Median ransom payment was $78,398 (+59% from Q4 2020)
- Average number of downtime days was 23 (+10 from Q4 2020)
- 77% of attacks include a threat to leak stolen data (up from 70% in Q4 2020)
Few law firms can survive the crippling of their primary software applications and denial of access to data for even a few days. While the news reports focus on large law firms, the Coveware report notes that small- and medium-sized law firms are vulnerable but most lack the financial resources to meet ransomware demands or to install robust cyber security systems.
Ransomware: How it works.
Ransomware is a type of software coded to infiltrate an organization’s computer operating system. The hackers spread their malware when team members collaborate or archive documents into folders or databases. Once the malware has reached critical mass, the hackers lock users out of access, download sensitive documents, and demand a ransom. In many cases, your law firm must pay the cybercriminals within a set amount of time or risk losing access forever.
Hackers attack by encrypting files at their endpoints or extensions. Examples include
- Microsoft files ending with PowerPoint .PPT, Word .doc and .docx, and Excel .xlsx, .xlsm, .xlsb, .xltx, and older extensions like s.xls, .xlt, and .xml
- Media flies ending with .mp4, .zip, .rar, and tar
- Database files ending with .sql, .accdb, .mbd, and .obd
- Imaging files ending with. ssd, .raw, .svg, and .psd
Other common hacker points-of-attack:
- Via email: “Malspam”, malicious attachments or links sent via email
- Via Testing Tools: Attacking testing tools like Cobalt Strike, Metasploit, or Mimikatz, to gain access to Active Directories and evade signature-based antiviruses
Work-in-progress documents are extra-vulnerable.
One of the weakest links in file security is works-in-progress: Word documents, Excel spreadsheets, data analytics reports, and videos, designs, and images that are undergoing review and alteration. For law firms, sharing of work-in-progress documents is a normal procedure for contract and claims preparation, M&A, IP submissions and dozens of other activities that require the expertise of multiple experts.
The COVID pandemic has accelerated collaboration on raw, work-in-progress documents among remote parties, whose site cybersecurity may be weak – thus providing hackers with vulnerable entry points for infiltrating your system and installing malware.
ShareVault DNFP protects work-in-progress documents.
Improving the security of unstructured, work-in-progress files is now possible by installing a protective layer: Dynamic Native File Protection (DNFP), a new type of security software provided by ShareVault, the company known for its ultra-secure virtual data room platform.
ShareVault DNFP software protects documents as they are being generated as well as when they are shared in collaboration. The DNFP administrator invites users to install DNFP, and then authorizes each user’s access and devices. The administrator can put a time limit on access, revoke authorization at any time, and can digitally “shred” documents on a user’s devices even after the user has left the team.
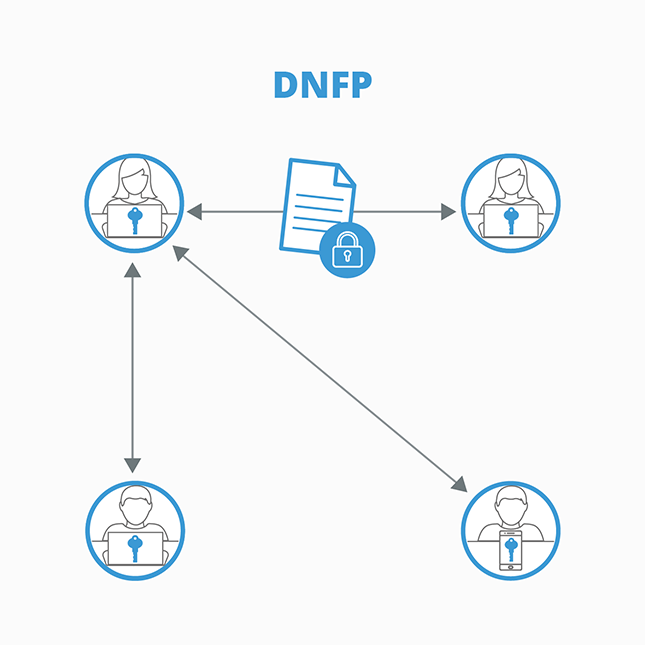
Cloud-based DNFP automatically installs at the computing operating system level – no IT team involvement is necessary. For users, simply click on a file and move it into a DNFP folder – no difficult learning curve.
DNFP provides protection for Word, Excel, PowerPoint, Photoshop, Illustrator, AutoCAD, SolidWorks, Cadence, and other productivity and design documents while they are in development and when they are shared – anywhere in the world. DNFP protects files regardless of how they are stored or shared – by email, Skype, Slack, DropBox, Google Drive, Microsoft 365, Zoom, et al. DNFP encryptions work for any device - desktops, laptops, phones, and tablets. And DNFP features auto-updates, to ensure users always have the latest iteration of protection.
ShareVault VDR protects archived documents.
A Virtual Data Room (VDR) is a cloud-based platform that stores documents and protects access and collaboration among authorized users. ShareVault’s industry-leading secure virtual data room protects sensitive “View Only” archived documents that are used in Due Diligence and other legal briefs, including client financials, HR data, board communications, data analytics, and third-party expert filings. The brief prep manager controls access by name of team member and by name of document, and can add additional protections such as two-step password authentication, Page-level Tracking, end-date permissions, and the ability to shred documents even when they have already been downloaded.
These control protections extend to remote parties, whose on-site cybersecurity protections are unlikely to be first-rate and thus are a potential entry point for hackers.
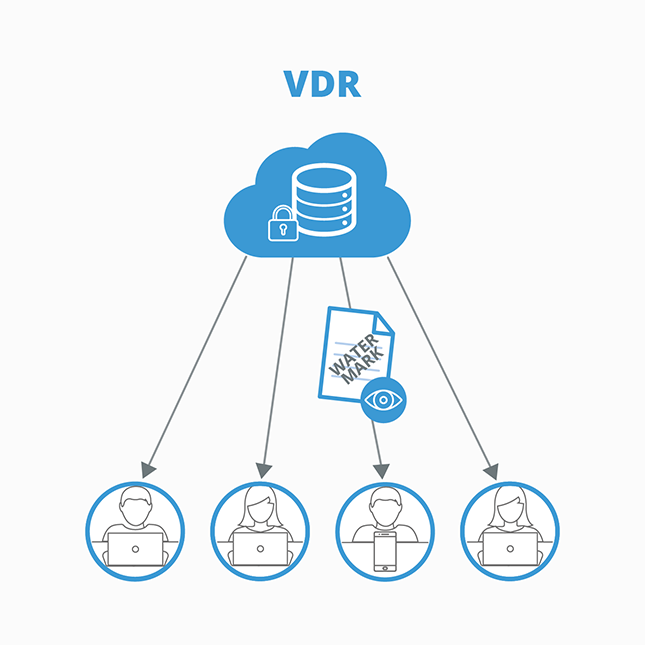
ShareVault’s VDR accommodates a wide range of interfaces and plug-ins and works seamlessly with DocuSign, Dropbox, Office 365, AutoCAD, Cadence, and other popular business applications.
Add more security to prevent ransomware:
Backup your data
The Multi-State Information Sharing and Analysis Center (MS-ISAC), a division of the Center for Internet Security (CIS), which works on cyber threat protection for government agencies, recommends backing up your files onto off-line servers, as backups to active files and those stored in the cloud. Your backup strategy should include storing multiple iterations of files, which will allow your organization to recover from an unencrypted version.
Install Email filters
Implement filters at your email gateway to block or erase emails with known malicious subject lines known and malspam indicators, and to block suspicious IP addresses. A further step is to filter inbound and outbound traffic based on IP addresses and ports.
Keep your system software up to date
Update your organization’s operating systems, applications, and software regularly. Turn on auto-updates to ensure automatic installation of the latest security patches, which can specifically address security gaps that hackers are seeking to exploit.
Be ready – Have a plan and train your staff
In today’s world, a cyberattack on your law firm is a statistical probability. Every firm needs what is called an “Incident Response Plan” to protect against an attack and to conduct the appropriate digital forensics should an attack occur. There are several firms that specialize in creating an Incident Response Plan for law firms.
The value of an Incident Response Plan goes beyond being a good business practice – it also helps illustrate compliance if the cyberattack makes your firm the target of legal action by clients or others who claim harm. The ABA Standing Committee on Ethics and Professional Responsibility published opinion “Lawyers Obligations After an Electronic Data Breach or Cyberattack” states that “the potential for an ethical violation occurs when a lawyer does not undertake reasonable efforts to avoid data loss or to detect cyber-intrusion, and that lack of reasonable effort is the cause of the breach… as a matter of preparation and best practices, lawyers should proactively develop an incident response plan with specific plans and procedures for responding to a data breach.”
Protect against ransomware: ShareVault!
For true state-of-the-art protection for both work-in-progress and archived documents, a company’s best choice is ShareVault’s combination of Dynamic Native File Protection (DNFP) and its Virtual Data Room (VDR) platform. DNFP and the VDR allow safe collaboration, even with remote parties, and dramatically reduces the risk of security breaches and vulnerability to ransomware attacks.
LEARN MORE
