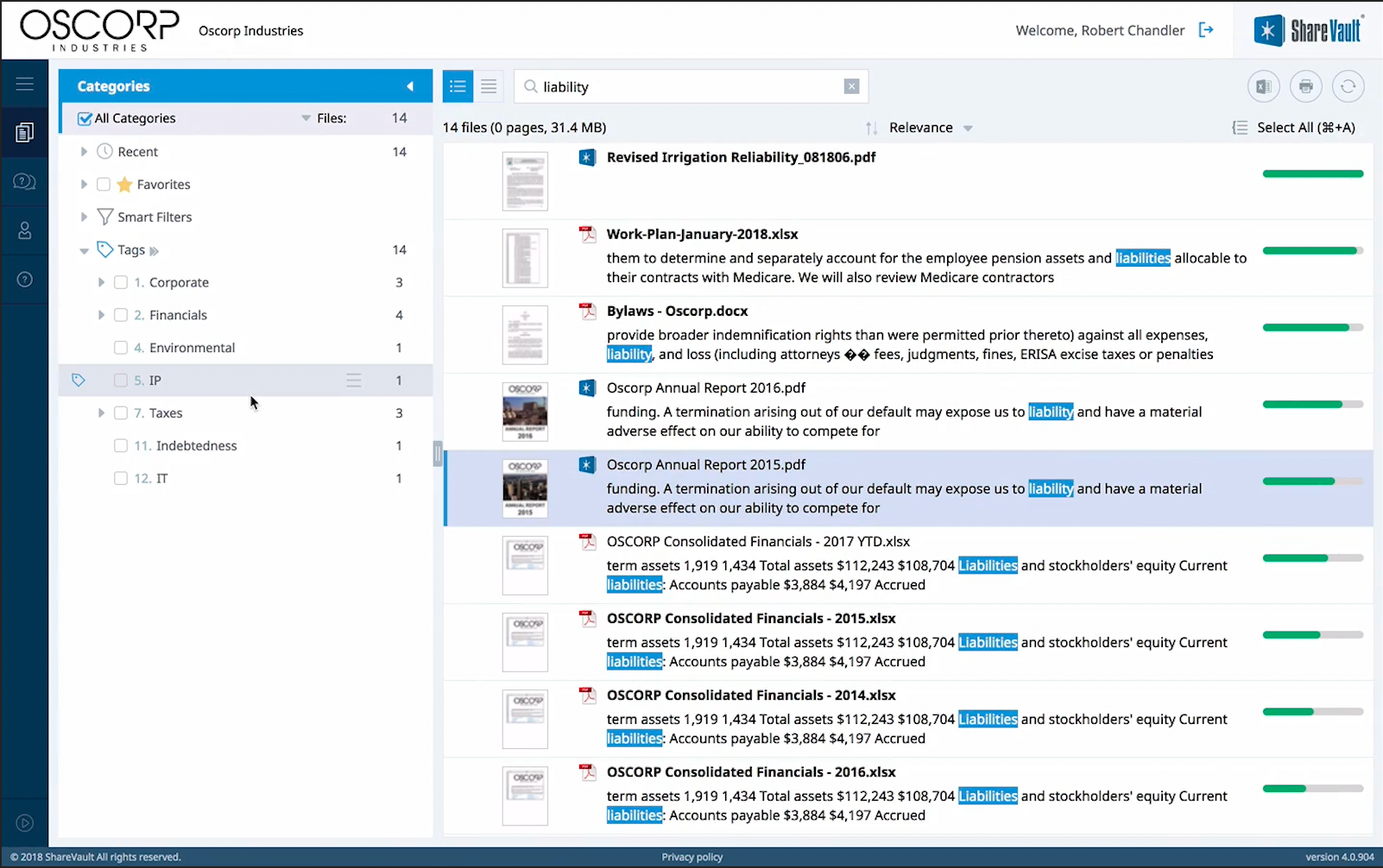
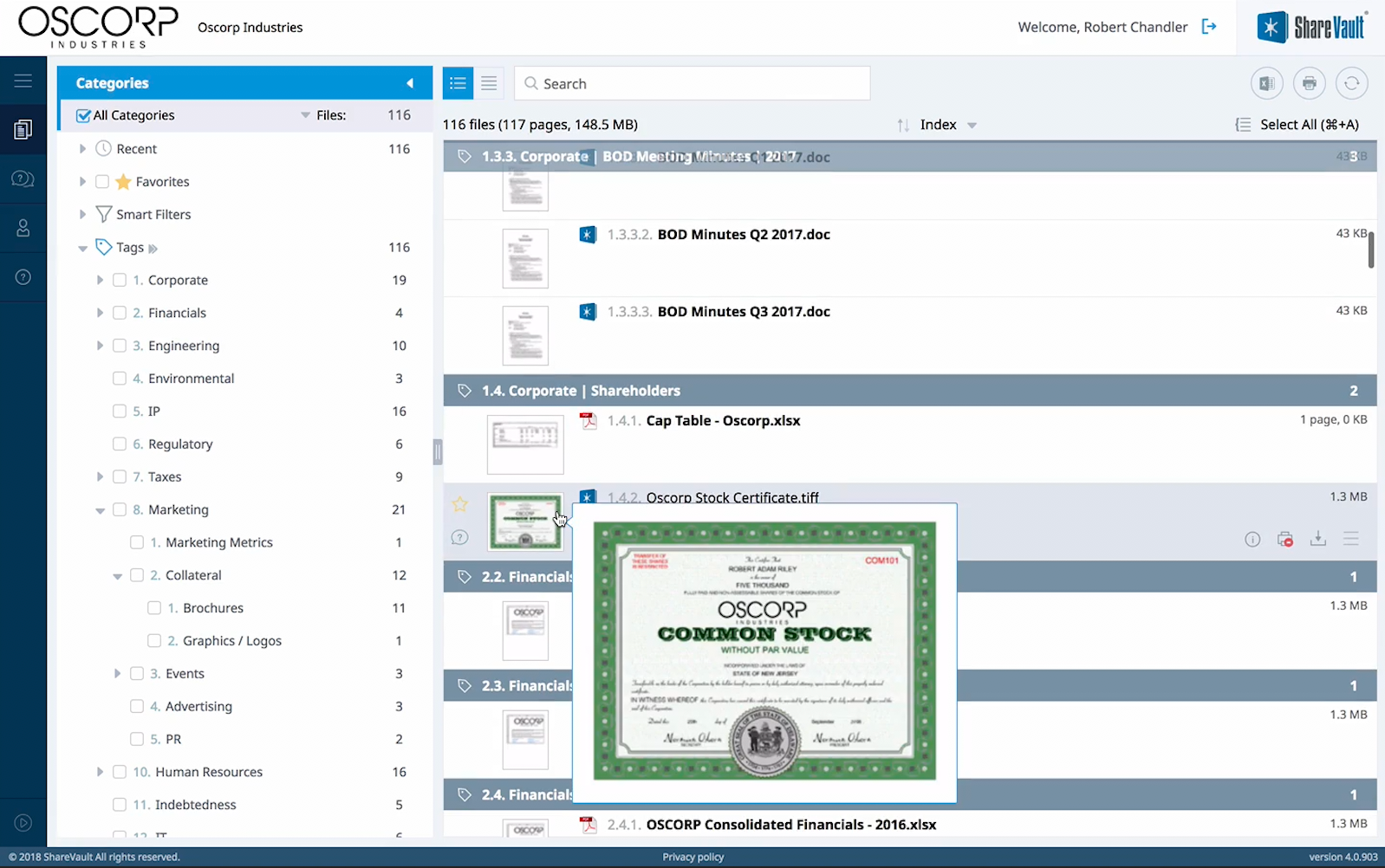
As security risks increase, leading organizations are taking more precautions to protect their documents from falling into the wrong hands. With ShareVault, your confidential business files will be afforded maximum protection, and you can organize and access them with the ultimate ease. Whether you're doing a deal with external parties or keeping your most important business files organized and secured within your organization, ShareVault allows you to rest assured that your important information is safe, so you can Focus On Your Business. Not On Software.
Below we've provided recommendations for selecting the ideal solution:
ShareVault protects your documents with multiple levels of encryption.
Certifications including SOC 1/2/3, PCI, ISO 90001 / 27001 / 27017 / 27018, FedRAMP Moderate, DoD CC SRG IL2, HIPAA, and HITRUST confirm that trusted third parties have verified the solution's adherence to the proclaimed security controls and their effectiveness.
Files should be encrypted at rest with AES-256, and all connections to them on the server should be via HTTPS over Secure Sockets Layer (SSL), providing AES-256 encryption in transit. Moreover, an Enhanced Validation (EV) certificate will provide further assurance that best practices have been followed for domain identity validation.